Hacking Code with Pure Math - Formal Verification
As penetration testers and software engineers, we spend a lot of time breaking things. We write unit tests, we run fuzzers, and we manually hammer APIs looking for edge cases. But there is always ...
As penetration testers and software engineers, we spend a lot of time breaking things. We write unit tests, we run fuzzers, and we manually hammer APIs looking for edge cases. But there is always ...
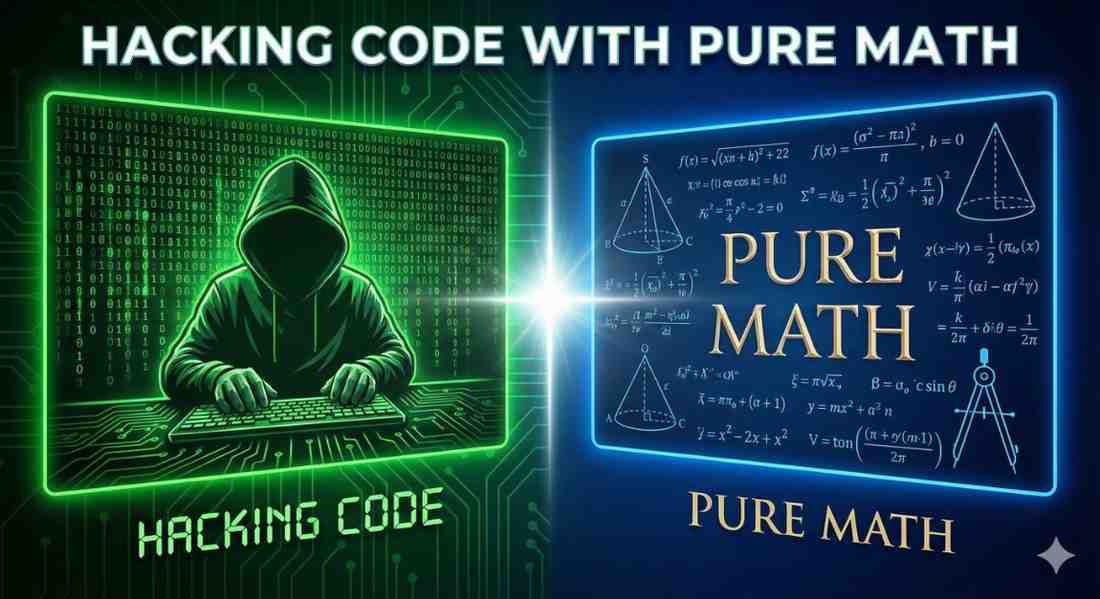
In our field—whether you are debugging a distributed system, hunting for security anomalies, or optimizing software performance—we are often drowning in data but starving for insights. "Data Analys...
The landscape of software development tools is undergoing a fundamental shift. For decades, our “intelligent” tools—IDEs, linters, and refactoring engines—were built on deterministic logic. Today, ...
In modern software engineering, we often find ourselves repeating the same patterns: setting up CRUD endpoints, defining database schemas, or writing serialization logic. As engineers, our instinct...
If you are studying software engineering or getting into Application Security, you know the pain of “Boilerplate.” You spend hours writing the same setup code—configuring firewalls, setting up data...
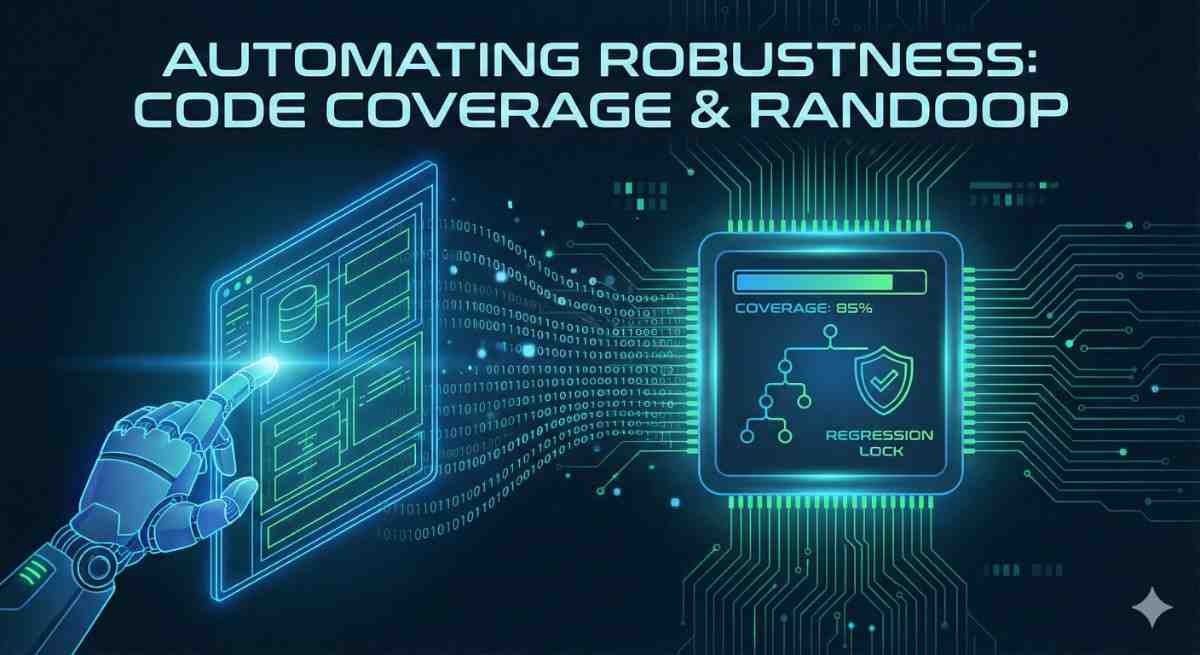
In modern software engineering, ensuring reliability goes beyond writing happy-path unit tests. As logic complexity increases, manual testing becomes insufficient for catching edge cases and state-...
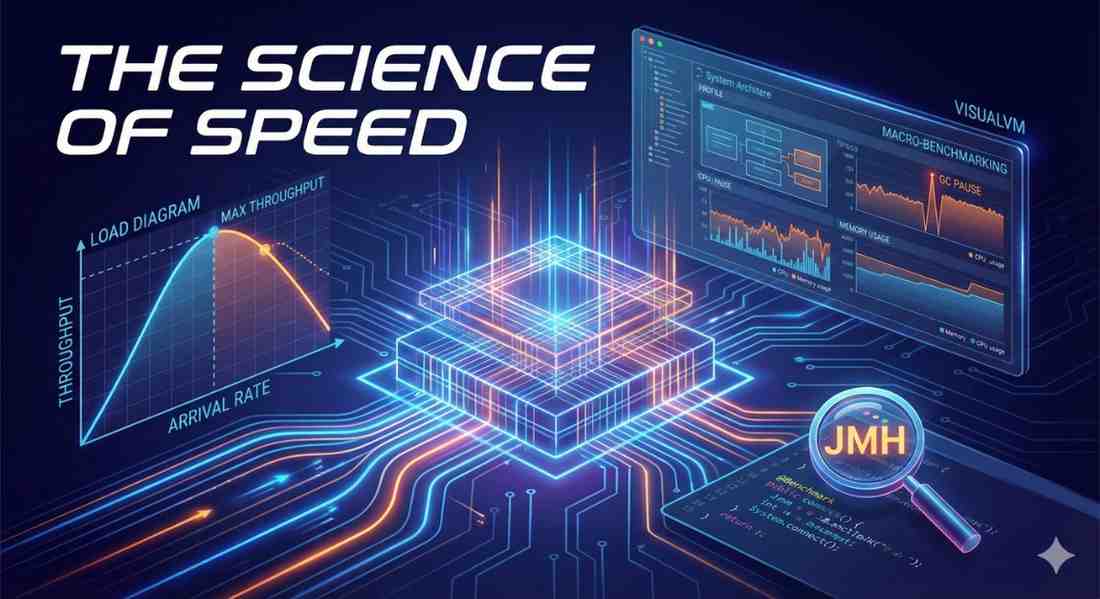
In software engineering, “fast” is a subjective term; “throughput of 10,000 operations per second” is an objective fact. However, deriving that fact requires more than just running a timer around a...
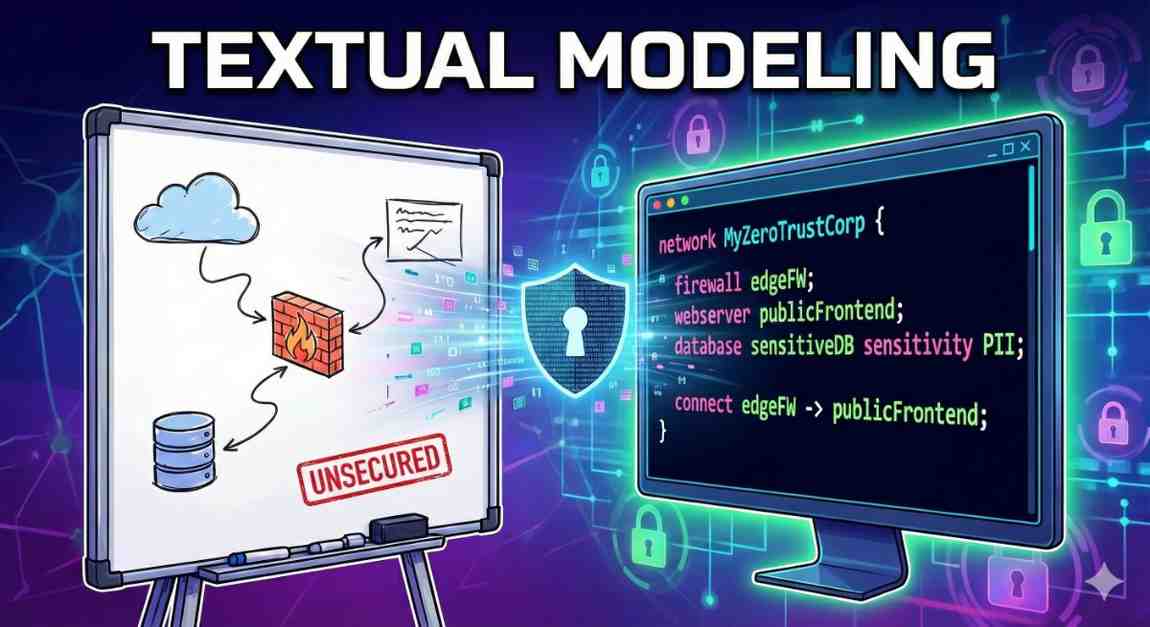
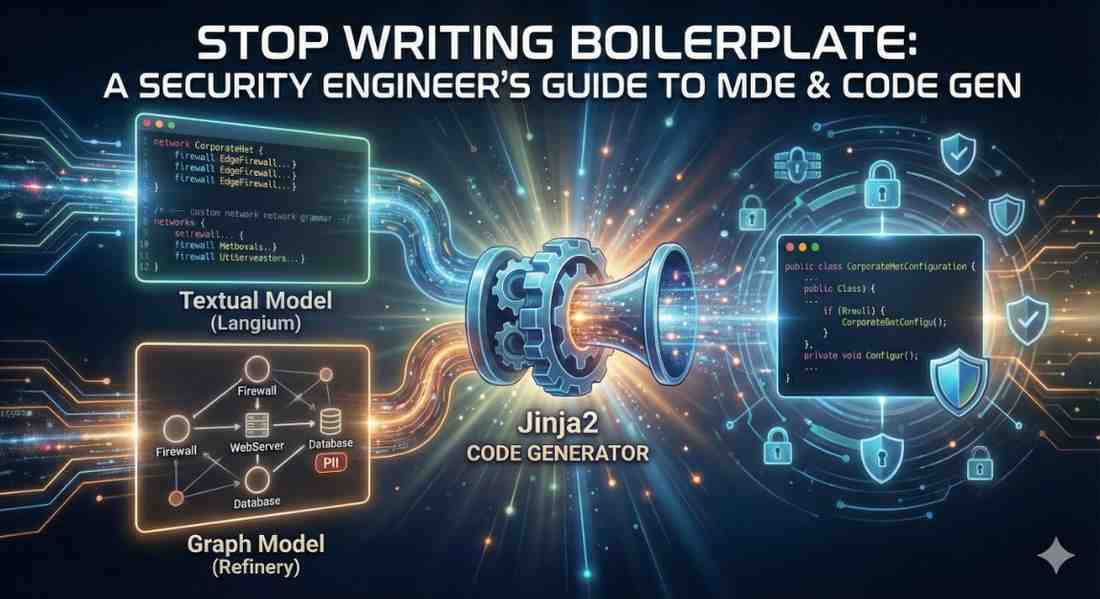
If you’ve followed my posts on penetration testing and app sec, you know the struggle of architectural diagrams. You draw a “Secure Network” on a whiteboard or in Visio: a Firewall here, a Database...
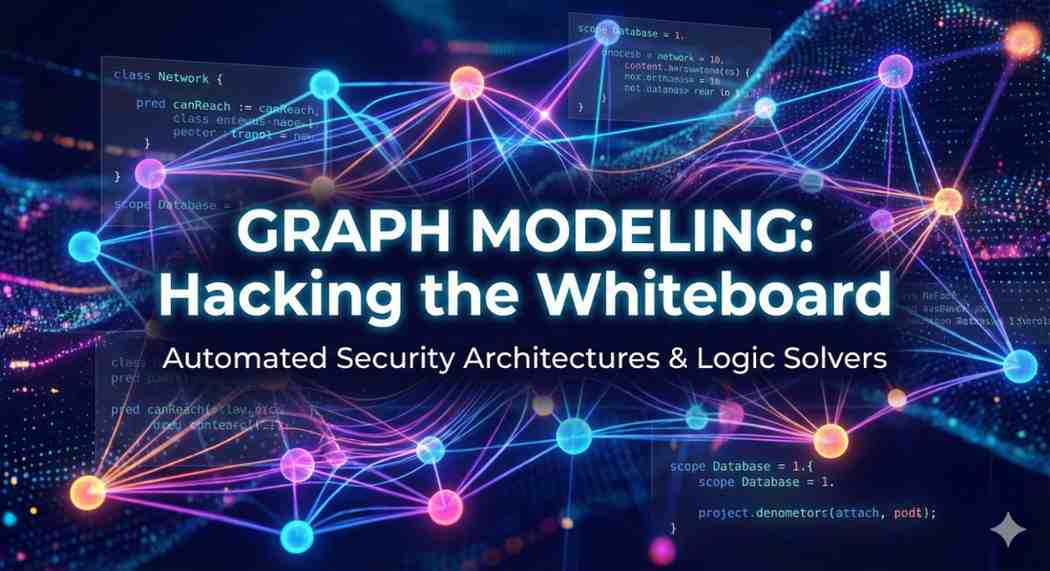
If you’ve ever tried to secure a complex system, you know the struggle: you draw a diagram on a whiteboard, you think it looks secure, but you missed one hidden path that allows an attacker to bypa...
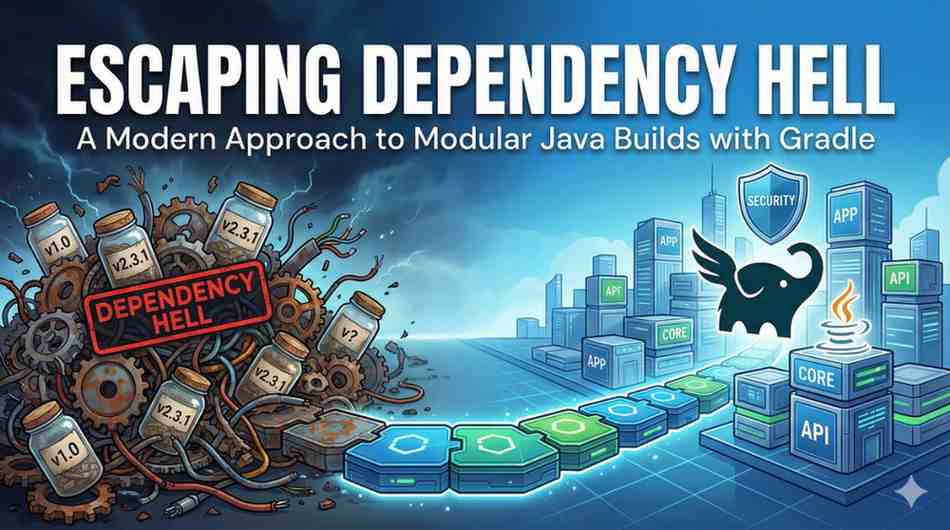
As software engineers and security practitioners, we often focus on the code itself—the logic, the vulnerabilities, the architecture. But the machinery that builds that code is often neglected. We’...